Google Cloud Launches an AI-Powered Agentic SOC With Mandiant Threat Intelligence
At RSAC 2026, Google Cloud unveiled an Agentic SOC where autonomous AI agents detect and respond to threats at machine speed, powered by Mandiant's frontline intelligence.
What an Agentic SOC Actually Means
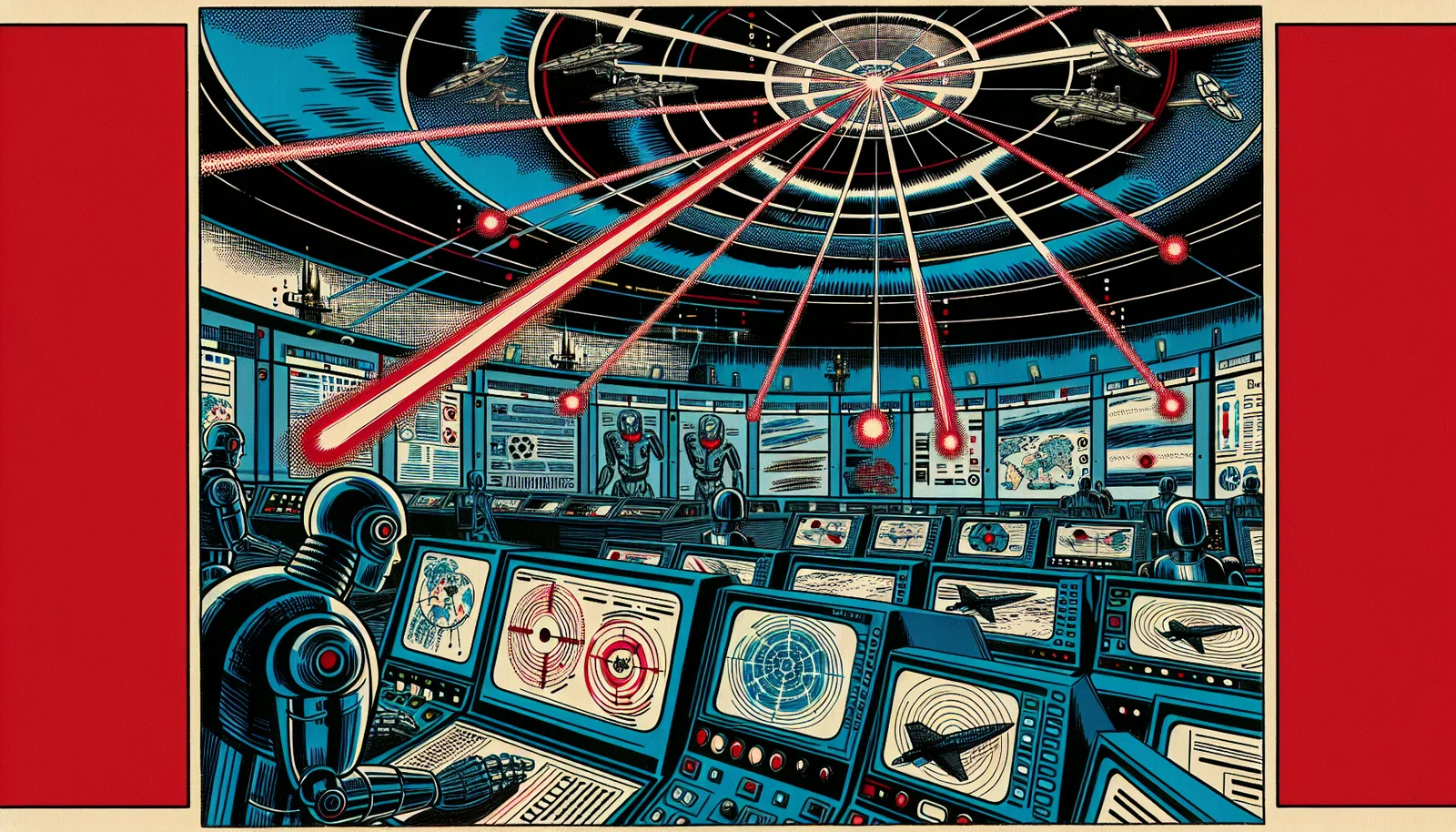
A traditional Security Operations Center runs on human analysts reviewing alerts, triaging incidents, and coordinating response. It is thorough but slow — and slow is the problem. Modern attack chains can move from initial access to lateral movement to data exfiltration in under 30 minutes. Human-speed triage does not scale to machine-speed threats.
At RSAC 2026 in San Francisco on March 23-26, Google Cloud unveiled its answer: an Agentic SOC that deploys autonomous AI agents to handle detection, investigation, and initial response without waiting for a human to pick up an alert queue. The system is powered by direct integration with Mandiant's frontline threat intelligence — not a quarterly threat report, but live knowledge from Mandiant's incident responders actively investigating breaches around the world.
How the Agentic SOC Works
The architecture is layered. At the base is Google Cloud's Security Command Center, which ingests security telemetry from cloud infrastructure, endpoints, network traffic, and identity systems. Above that, autonomous AI agents — purpose-built for specific tasks — operate on that telemetry continuously: one agent class handles initial alert triage and correlation, another investigates suspicious activity by querying relevant logs and threat intelligence, a third evaluates containment options and can execute pre-approved response playbooks automatically.
The key differentiator is the Mandiant integration. When an autonomous agent investigates a suspicious activity pattern, it has direct access to Mandiant's threat intelligence database — including indicators of compromise, attacker tactics and techniques, and active campaign data from Mandiant's global incident response engagements. An agent investigating a suspicious PowerShell execution pattern is not querying a generic threat database; it is querying knowledge built from thousands of real breach investigations.
Chrome Enterprise Gets AI Tool Governance
Google also announced new Chrome Enterprise security controls specifically targeting unsanctioned AI tool usage — an emerging risk category that security teams are increasingly contending with. Enterprise employees using personal AI accounts or browser-based AI extensions can inadvertently expose sensitive data to third-party AI services outside the organization's data governance framework.
The new Chrome Enterprise controls allow security teams to detect and block data flows to unsanctioned AI services, applying the same data loss prevention logic to AI tool usage that has historically governed USB drives and cloud storage services. Keylogging protection at the browser level has also been enhanced to prevent malicious extensions from capturing credentials or sensitive input.
The M-Trends 2026 Foundation
Underpinning Google's RSAC announcement is the M-Trends 2026 report from Mandiant — the annual flagship threat intelligence publication that documents attacker behavior trends across Mandiant's global incident response engagements. The 2026 report informed the specific capabilities prioritized in the Agentic SOC's initial deployment, creating a direct line from observed attacker behavior to automated defensive response design.
For security teams evaluating whether to trust autonomous agents with detection and response decisions, this grounding in real-world threat data matters. The agents are trained on how actual attackers have actually behaved across thousands of real incidents — and that specificity is what separates a genuinely effective autonomous SOC agent from one that generates false positives and erodes analyst trust.
Where attacker speed exceeds human response speed, autonomous defense is not optional. It is the only defense that keeps pace.
Sources: [Google Cloud Blog](https://cloud.google.com/blog) (March 23-26, 2026), [GovTech RSAC Highlights](https://www.govtech.com) (March 2026), [SecurityWeek](https://www.securityweek.com) (March 2026)
