Pakistan-Linked APT36 Floods Indian Government Networks With AI-Generated 'Vibeware' Malware
Bitdefender reveals a nation-state campaign using AI coding assistants to mass-produce disposable malware in 12+ languages, overwhelming defenders with sheer volume.
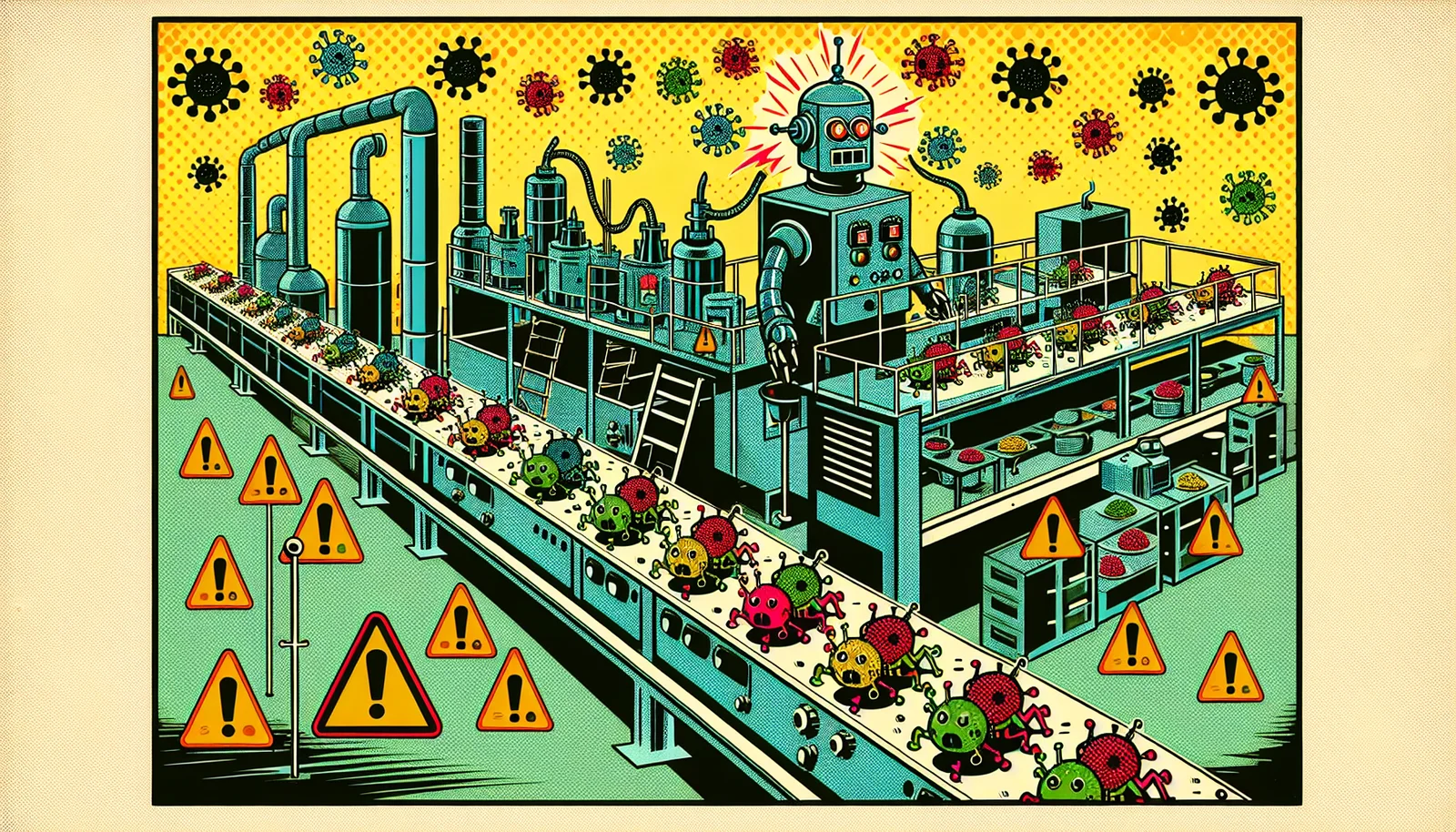
Quantity Over Quality — By Design
The cybersecurity industry just got a new term to worry about: "vibeware." Bitdefender researchers have published a detailed report revealing that APT36, a Pakistan-linked threat group also known as Transparent Tribe, has adopted AI coding assistants to mass-produce disposable malware implants at an industrial scale — churning out new variants at a near-daily cadence from late December 2025 through February 2026.
The targets were Indian government agencies and diplomatic missions abroad. But unlike traditional nation-state operations that invest months in crafting sophisticated, bespoke tools, APT36's new approach is deliberately crude: generate as many different implants as possible, in as many different programming languages as possible, and overwhelm defenders with volume.
Twelve Languages, One Strategy
The campaign deployed over 12 distinct malware families written in Nim, Zig, Crystal, Rust, Go, and C# — languages chosen specifically because most security tools have limited detection signatures for them. Notable tools include Warcode (a Crystal-based shellcode loader), LuminousCookies (a Rust-based Chromium cookie stealer that bypasses App-Bound Encryption), and SheetCreep (which uses Google Sheets as a command-and-control channel).
The command-and-control infrastructure is equally distributed, routing traffic through Discord, Slack, Google Sheets, Supabase, Firebase, and Google Drive — all legitimate services that make network-level detection extremely difficult. Bitdefender frames this approach as "Distributed Denial of Detection" — the attacker's bet that even if defenders catch one implant, the other eleven will persist.
The AI Fingerprints
The AI-assisted nature of the malware is evident in its flaws. One Go binary shipped with placeholder template text where server URLs should have been — the tool was literally incapable of exfiltrating data because nobody reviewed the AI's output. Binaries contain Unicode emoji strings in logging output and compile metadata pointing to AI-assisted development environments. The code quality is inconsistent, but the production speed is unprecedented.
This is one of the first well-documented cases of a nation-state actor systematically using AI to industrialize malware production. The quality is low, but the volume and diversity are the point.
Sources: Bitdefender (March 7, 2026), Dark Reading (March 7, 2026), Hackread (March 7, 2026)
